Learn how to use residential proxies for social media management at scale. Platform-specific strategies, account warming, IP assignment, and risk avoidance guide.
Why Social Platforms Crack Down on Multi-Account Operations
The core problem platforms face is manipulation at scale. Bot networks, coordinated inauthentic behaviour, spam rings, fake engagement operations, all of it rests on controlling many accounts from few operators. Platform integrity teams at Meta, TikTok, and X have seen what unchecked multi-accounting does: astroturfed political movements, fraudulent product reviews, engagement farms that devalue real interaction, spam that degrades the user experience.
The collateral damage of those anti-abuse measures lands hard on legitimate operators. A digital marketing agency managing accounts for 40 clients needs access to all of them, usually from the same office. A global brand running regional Instagram accounts for 25 markets switches between them daily. A social analytics company monitors thousands of public profiles for clients. None of them are bad actors, but their activity patterns, multiple accounts, frequent switching, high-volume access from shared IPs, mirror exactly what abuse detection systems are built to flag.
Platforms don't distinguish intent, only patterns. Their automated systems flag multi-account activity whether it's a spam operation or a Fortune 500 brand managing regional presence. That's why proxies aren't optional for scaled social media management, they're the foundational infrastructure that makes the operation technically viable.
How Platforms Detect Multi-Account Activity
IP correlation. The most basic detection: multiple accounts logging in from the same IP. Platforms maintain login-IP mapping tables and flag accounts that share IPs with others, especially when combined with other signals. A single shared IP usually isn't grounds for immediate action, but it raises a risk score that makes other signals more likely to trigger enforcement.
Device fingerprinting. Platforms fingerprint the device behind each account: browser type, screen resolution, installed fonts, GPU renderer, timezone, language settings. When multiple accounts share identical fingerprints, the correlation is strong evidence of multi-accounting. Mobile apps collect even more device signals, hardware IDs, installed app lists, sensor data.
Behavioural analysis. Machine learning models evaluate how accounts behave. Do they follow the same users? Like the same content? Post at suspiciously regular intervals? Respond to each other's content disproportionately? Behavioural clusters of accounts acting in concert get flagged for review, even if they use different IPs and devices.
Login pattern analysis. Rapid sequential logins to multiple accounts from the same IP or device, the exact pattern of an agency worker switching between client accounts, triggers alerts. Geographic impossibility also gets flagged: logging into one account from London and another from Tokyo within minutes suggests both accounts are controlled by the same operator using proxies, which is exactly the conclusion you want to avoid.
Cookie and storage tracking. Browser localStorage, IndexedDB, and cross-origin cookies can link accounts that share a browser instance. Platforms embed tracking identifiers in local storage that persist across account switches.
Why Residential Proxies Are Non-Negotiable for Multi-Account Management
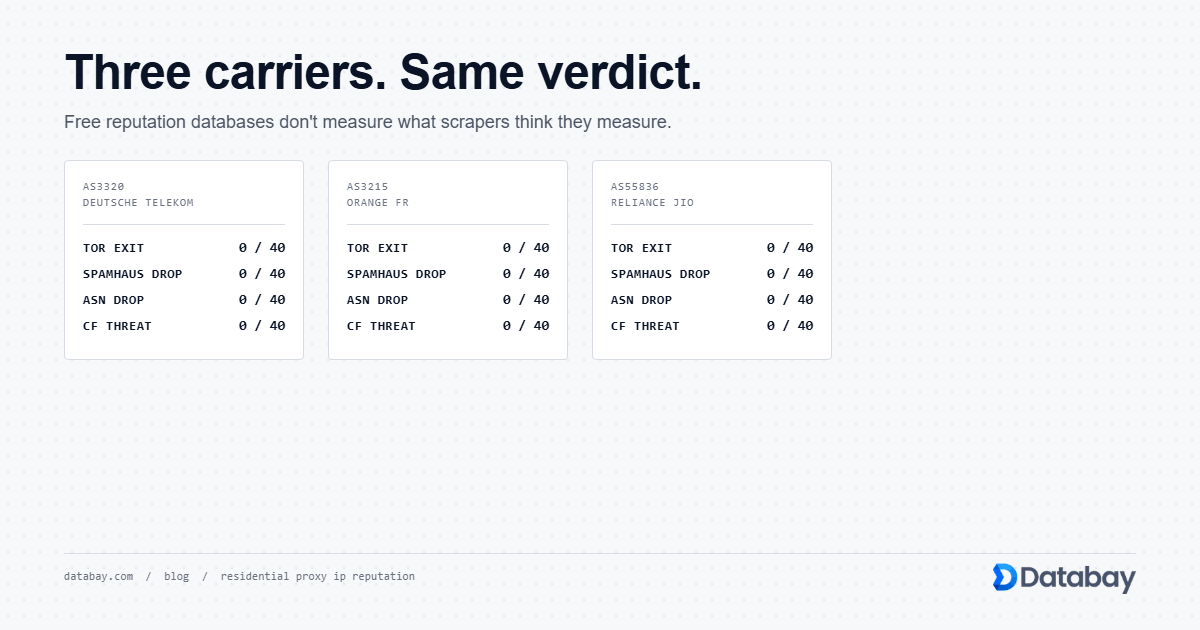
VPN IPs face the same problem. Every major VPN provider's IP ranges are catalogued in commercial detection databases. The arms race between VPN providers acquiring new IPs and platforms blocking them is continuous, but the platforms are winning. Using a VPN for multi-account management means constant disruption as IPs get flagged.
Residential proxies bypass this entire classification layer because the IPs belong to real ISPs. When Instagram checks whether an IP is datacenter, VPN, or residential, a residential proxy IP returns 'residential' because it genuinely is a residential IP. No false classification involved. The IP is exactly what it appears to be.
The practical impact is real. Accounts accessed through residential proxies experience dramatically lower rates of verification challenges, temporary locks, and permanent bans compared to datacenter or VPN connections. For an agency managing 50+ client accounts, the difference between a 20% weekly challenge rate on datacenter proxies and a 1% rate on residential translates directly to operational efficiency and client satisfaction.
This isn't a nice-to-have optimisation. For any operation managing more than a handful of social media accounts, residential proxies are the minimum viable infrastructure.
Platform-Specific Proxy Strategies: Instagram and Meta
Instagram. The platform tracks IP-to-account mappings aggressively. Using the same IP for more than 2 or 3 accounts within a short window will trigger action, starting with soft locks requiring phone verification, escalating to temporary restrictions and eventual permanent bans. Instagram's mobile app collects device-level telemetry that supplements IP data, which means browser-based management through proxies is actually safer than app-based management in some scenarios.
For Instagram specifically, mobile proxies outperform residential. Instagram's detection expects real mobile network IPs for app interactions. A residential IP accessing Instagram's mobile API endpoints isn't inherently suspicious but stands out slightly against expected mobile network traffic. Genuine 5G/4G mobile proxy IPs match the expected traffic profile perfectly.
Assign one dedicated IP per Instagram account and keep that assignment permanent. Instagram correlates login IPs over time. An account that has always logged in from a Comcast IP in Dallas and suddenly switches to a BT IP in London triggers a security review. Consistency matters more than IP quality.
Facebook. Facebook tracks the combination of IP address, device fingerprint, and browser cookie. Changing any one triggers additional verification. Changing two or more at once almost guarantees a challenge. Managing Facebook accounts through proxies, maintain consistent browser profiles per account: same cookies, same fingerprint, same proxy IP. Use Facebook's Business Manager for legitimate multi-account scenarios where possible, it's the official framework for agency-style multi-account access.
Platform-Specific Proxy Strategies: TikTok, X, and LinkedIn
X (Twitter). X ties rate limits directly to IP addresses. Each IP gets a specific number of API calls, page loads, and actions per time window. Running multiple accounts through one IP means they share that rate limit, which causes failures and triggers scrutiny when limits are hit. The solution: one residential IP per account, with usage that stays well within normal individual limits. X is less aggressive on device fingerprinting than Instagram or TikTok, making it more forgiving for browser-based management. Rapid follower growth, aggressive posting, and repetitive content patterns will trigger account-level flags regardless of proxy quality.
LinkedIn. LinkedIn is exceptionally strict on automation and runs one of the lowest tolerances for multi-accounting. The platform actively detects and bans accounts that use automation tools, even for legitimate outreach. Connection request limits are hard-capped, and exceeding them, even slowly, gets you restricted. For LinkedIn, residential proxies have to be paired with extremely conservative activity levels. Never exceed 50 to 80 connection requests per day per account. Use sticky residential IPs that match the account's stated location. LinkedIn is the one platform where less activity through a good proxy consistently outperforms more activity through any proxy.
Proxy Assignment Strategy: One Account, One Identity
Sticky session configuration. Use sticky residential IPs with long session durations. The standard 10-minute sticky session used for web scraping isn't enough for social media. You need the same IP assigned to the same account for days or weeks. Most quality proxy providers offer long-duration sticky sessions or dedicated residential IPs for exactly this use case. At Databay, session durations can be configured to keep the same IP for extended periods, which is essential for social media account consistency.
Geographic matching. Match the proxy IP's location to the account's stated location. If a client's Instagram account claims to be a restaurant in Chicago, access it through a Chicago residential IP. If a brand runs a UK-focused X account, use a UK residential IP. Geographic inconsistency between the account's content and access IP is a correlation signal detection systems flag.
IP isolation. Never reuse the same IP across different social media accounts. An IP that appears in the login history of two Instagram accounts creates a permanent link between them. If one account is flagged for any reason, the linked account is at risk. Maintain a strict mapping: Account A always uses IP A, Account B always uses IP B, assignments never cross.
Documentation. Maintain a ledger of account-to-IP assignments. Include the IP address, proxy provider, assigned account, platform, geographic target, and assignment date. When IPs need to rotate due to provider changes, transition gradually, log in from the new IP while the old IP is still recent in the account's history, to avoid a sudden geographic jump.
Warming Up New Accounts Without Getting Flagged
Day 1 to 7: Minimal activity. Log in once or twice daily from the dedicated residential IP. Complete profile setup, photo, bio, links, over several sessions, not all at once. Follow 5 to 10 accounts a real user in that niche would naturally follow. Don't post content. Don't send messages. Don't interact aggressively. The goal is an IP-to-account history that looks like a real person setting up their profile.
Day 8 to 21: Gradual engagement. Begin posting content, once per day maximum. Like and comment on posts in your niche, but cap at 10 to 20 interactions per day. Follow 5 to 15 new accounts per day. Respond to any engagement your posts receive. Every action comes from the same residential IP. Timing should vary. Not robotic 24-hour intervals. Realistic patterns: posting during local business hours, occasional evening engagement, weekend gaps.
Day 22 to 60: Normal growth. Gradually increase posting frequency toward your target cadence (2 to 3 posts per day maximum). Scale following and engagement proportionally. Start using platform features beyond basic posting: Stories, Reels, Polls, Spaces. By this point the account has an established IP history, consistent device fingerprint, and believable engagement pattern.
Day 60+: Full operation. The account has passed the high-scrutiny window. Keep using the same dedicated proxy IP. Maintain realistic activity levels. Even established accounts can be flagged if activity suddenly spikes to abnormal levels.
The single most common mistake agencies make is rushing this. Skipping warmup to meet a client deadline costs more time in account recovery than the warmup would have taken.
Content Scheduling and Posting Through Proxies
Consistent IP during posting sessions. When your scheduling tool posts content to a platform, it has to use the same residential IP assigned to that account. If your tool cycles through proxy IPs randomly, each post appears to come from a different location, a pattern no individual user would exhibit. Configure your posting tool to maintain IP affinity per account.
Timezone-appropriate posting. If your proxy IP is in Los Angeles but your scheduling tool posts at 3 AM Pacific, the discrepancy is subtle but detectable. Align your posting schedule with normal waking hours in the proxy IP's timezone. That doesn't mean you can't schedule overnight posts, real users schedule content too, but the bulk of activity should happen during reasonable hours for the proxy's location.
Rate limiting at the tool level. Even with a perfect proxy setup, posting too frequently trips platform rate limits. Build delays between actions into your scheduling tool: 30 to 60 seconds between consecutive posts to different accounts, 5 to 10 seconds between actions within a single account. Delays should have random variability. Exactly 30 seconds between every action is a bot signature. 27 to 45 seconds with natural distribution is not.
Error handling. When a proxy connection fails mid-posting, your tool has to pause rather than retry through a different IP. A post that fails from one IP and immediately succeeds from another is a multi-account signal. Wait for the assigned IP to come back, or escalate the failure for manual review rather than automatically switching proxies.
Monitoring and Analytics Collection Across Regions
Regional content visibility. Social algorithms serve different content to users in different locations. A post's visibility, engagement, and reach vary by viewer location. To understand how your client's content performs in the UK vs Germany vs Japan, you need to view the platform from IPs in each of those countries. Residential proxies give you this multi-regional view without staffing each market.
Competitor monitoring. Tracking competitor activity across regional accounts means accessing those accounts as a local user. Some competitors run region-specific campaigns visible only to local audiences. Without proxies in the target region, you only see their global content and miss localised promotions, pricing, and messaging that may be directly relevant to your client's strategy.
Ad creative verification. Social advertising platforms serve different ad creatives based on viewer location, demographics, and behaviour. Verifying your client's ads appear correctly in target markets means accessing the platform from those markets. Residential proxies let you verify ad delivery, placement, and rendering from the audience's perspective in each target geography.
Hashtag and trend monitoring. Trending topics and hashtag performance are heavily regionalised. A hashtag trending in Brazil may not show up in US trending lists. Monitoring regional trends through local residential IPs gives accurate, location-specific trend data that feeds content strategy for regional accounts.
For all these monitoring cases, rotating residential IPs work well since you're observing rather than managing accounts. No account consistency requirement. You just need to appear as a local user in each target market.
Anti-Detect Browsers: The Essential Companion to Proxies
Tools like Multilogin, GoLogin, and AdsPower create isolated browser profiles, each with its own unique fingerprint: different canvas hash, WebGL renderer, screen resolution, timezone, language, user agent, installed fonts. Each profile also maintains its own cookies, localStorage, and IndexedDB, which prevents cross-account contamination through browser storage.
The workflow is straightforward. Create one browser profile per social media account. Assign a dedicated residential proxy to each profile. Always access that account through its designated profile. To the platform, each profile-proxy combination looks like a completely different person on a completely different device in a completely different location.
Profile configuration matters. Don't use randomised fingerprints. They can produce impossible combinations (like a Linux user agent with a DirectX GPU renderer). Use fingerprints modelled on real device populations. Good anti-detect browsers base their fingerprint generation on actual device telemetry, producing combinations that exist in the wild.
Match fingerprint to proxy location. If your proxy IP is in Germany, your browser profile should report a German timezone (Europe/Berlin), German language (de-DE), and a screen resolution common in the German market. These consistency details matter because platforms cross-reference signals. A US timezone with a German IP is a minor red flag that adds to the account's risk score.
The cost of anti-detect browsers is a direct operational expense, typically $100 to $400 per month depending on profile count, but the cost of losing accounts due to fingerprint correlation is far higher.
Critical Mistakes That Get Accounts Banned
- Sudden IP changes. Switching an account's proxy IP without a gradual transition triggers security reviews. If you must change an IP, do it during a natural gap in activity and log in once or twice from the new IP before resuming full operations.
- Too many accounts per IP. Running more than one social media account per residential IP is the single most common cause of linked-account bans. When one account is actioned, every account sharing its IP history is at risk. The cost savings of sharing IPs don't survive the first ban wave.
- Unrealistic activity volumes. A new account posting 10 times per day, following 200 accounts, and liking 500 posts is obviously automated regardless of how good the proxy is. Platforms set internal activity thresholds that, when crossed, move an account from passive monitoring to active investigation.
- Identical content across accounts. Posting the same content to multiple accounts, even with slight variations, creates a content fingerprint that links the accounts. Platform content hashing is sophisticated enough to detect light rewording and image similarity.
- Running engagement groups. Coordinated engagement, groups of accounts that systematically like, comment on, and share each other's content, gets detected through graph analysis. Platforms map interaction networks and identify clusters of accounts that engage with each other disproportionately.
- Ignoring platform updates. Detection systems evolve continuously. A strategy that worked six months ago may be ineffective today. Monitor platform policy updates, stay current with anti-detection communities, and test changes with low-value accounts before applying them to important ones.
Scaling Operations: From 10 Accounts to 500
10 to 25 accounts. Manual management is feasible. One anti-detect browser, individual proxy assignment, a spreadsheet tracking accounts-to-IPs. One person can handle the operational overhead. Proxy costs are modest, 25 dedicated residential IPs represent a manageable monthly expense.
25 to 100 accounts. You need systematic tooling. Manual proxy assignment becomes error-prone. Invest in a social media management platform that integrates proxy configuration per account. Automated warmup sequences save time and reduce human error. At this scale you likely need a mix of residential and mobile proxies. Residential for most platforms, mobile for Instagram accounts that use app-based features heavily.
100 to 500 accounts. Enterprise territory. Your proxy provider relationship becomes a critical vendor partnership. You need guaranteed IP pool depth in target countries, high uptime, and responsive support for IP-related issues. Proxy costs become a significant line item, and optimising the residential-vs-mobile mix directly impacts margins. Automated monitoring that alerts when an account faces a challenge or ban becomes essential. Manually checking 300 accounts daily isn't viable.
At every scale the fundamental principles stay the same: one IP per account, geographic consistency, realistic activity levels, isolated browser environments. What changes is the infrastructure needed to keep those principles running across hundreds of accounts without manual oversight breaking down.
Databay's infrastructure supports that scale with large residential IP pools across 200+ countries, configurable sticky sessions, and the throughput for concurrent multi-account operations.