Are proxies legal? This compliance guide covers proxy legality by jurisdiction, key court rulings, permitted use cases, and best practices for businesses.
The Short Answer: Proxies Are Legal Networking Tools
The confusion around proxy legality comes from a basic mistake: conflating the tool with its application. A kitchen knife is legal. Using one to commit a crime is not. The same principle applies to proxies. The proxy itself is neutral infrastructure. What determines legality is how you use it, what data you collect, and whether you break specific laws or contractual obligations in the process.
For businesses, this distinction matters enormously. Competitive intelligence teams, ad verification firms, cybersecurity researchers, and pricing analysts all rely on proxies as standard operational tools. The question is never "can we use proxies" but "are we using them within the boundaries of applicable law?"
US Law: The CFAA and Its Boundaries
The landmark 2021 Supreme Court ruling in Van Buren v. United States significantly narrowed the CFAA's scope. The Court held that "exceeding authorized access" applies only to those who access information they aren't entitled to obtain. It does not apply to people who misuse information they are otherwise permitted to view. This ruling drew a clearer line: accessing publicly available web pages through a proxy doesn't constitute a CFAA violation, even if the website operator would prefer you didn't.
Several state-level computer fraud statutes mirror the CFAA with varying degrees of breadth. California's Complete Computer Data Access and Fraud Act (Penal Code 502) and Virginia's Computer Crimes Act are notable examples. Businesses operating across multiple states should be aware that state-level exposure can differ from federal standards, though the general trend since Van Buren has been toward narrower interpretation.
The hiQ Labs v. LinkedIn Ruling and Public Data Scraping
The Ninth Circuit ruled in hiQ's favour in 2022. Scraping publicly accessible data on the internet doesn't constitute accessing a computer "without authorization" under the CFAA. The court reasoned that public websites are analogous to open stores: anyone can enter, and the owner cannot retroactively criminalise entry simply by sending a letter.
This ruling established several key principles for businesses using proxies:
- Accessing publicly available data is not a CFAA violation, even if the website operator objects
- A cease-and-desist letter alone does not create "authorization" barriers under the CFAA
- Technical blocking measures (like IP bans) do not transform public data access into unauthorised access
The ruling is binding only in the Ninth Circuit. Other circuits may interpret the law differently. The Supreme Court declined to hear LinkedIn's appeal, leaving the Ninth Circuit decision intact but not establishing nationwide precedent.
EU Law: GDPR and the Personal Data Question
If you use proxies to scrape European websites and the data you collect contains personal information (names, email addresses, photos, employment details, even IP addresses), you are processing personal data under the GDPR. That triggers obligations: a lawful basis for processing, transparency notices for data subjects, and potentially a Data Protection Impact Assessment (DPIA).
The lawful basis most commonly invoked for web scraping is "legitimate interest" under Article 6(1)(f). That requires a three-part balancing test: the interest must be legitimate, the processing must be necessary for that interest, and the interest must not be overridden by the data subject's rights. Competitive price monitoring on B2B product pages generally passes. Scraping personal profiles for marketing databases generally does not.
The Clearview AI cases across multiple EU jurisdictions illustrate the risk. Clearview scraped billions of publicly available facial images and was fined by regulators in France (20 million euros), Italy (20 million euros), Greece (20 million euros), and the UK (7.5 million pounds). The data was public. The fines were still enormous.
Terms of Service: Contractual vs. Criminal Liability
The short answer, post-Van Buren, is no. Violating a website's Terms of Service is a contractual matter, not a criminal one. The Supreme Court explicitly rejected the idea that ToS violations constitute "exceeding authorized access" under the CFAA. A website can sue you for breach of contract if you violate its ToS, but it cannot have you prosecuted under federal computer crime statutes simply for that violation.
That said, contractual liability is still liability. A breach-of-contract claim can result in injunctive relief (a court order to stop scraping), compensatory damages, and in some cases specific performance. The practical risk depends on several factors:
- Whether the website operator has the resources and motivation to pursue litigation
- Whether your scraping caused demonstrable harm (server load, competitive damage)
- Whether you collected proprietary or copyrighted content versus factual data
- The jurisdiction and specific ToS language
For most businesses running legitimate competitive intelligence on public pricing data, product listings, or market trends, the practical risk of ToS-based litigation is low. For businesses scraping at massive scale, extracting proprietary databases, or competing directly with the scraped site, the risk is materially higher.
Activity-by-Activity Legal Status
Competitive Price Monitoring Generally legal. Collecting publicly displayed prices from competitor websites is standard business practice. Courts have consistently held that published prices are factual data not subject to copyright. Risk level: low.
Ad Verification Legal and industry-standard. Brands and agencies use proxies to verify that their advertisements appear correctly across geographies and publishers. A widely accepted, non-controversial use case. Risk level: minimal.
SEO and SERP Monitoring Generally legal. Checking search engine results pages from different locations to monitor rankings is standard marketing practice. Risk level: low.
Web Scraping of Public Data Legal in most jurisdictions for factual, non-personal data. Subject to GDPR constraints in the EU if personal data is involved. Risk level: low to moderate depending on data type and jurisdiction.
Market Research and Aggregation Generally legal for public data. Travel fare aggregation, real estate listing monitoring, and similar use cases have strong legal footing after hiQ. Risk level: low to moderate.
Bypassing Authentication or Access Controls Potentially illegal. If a website requires login credentials and you circumvent that requirement, you may be violating the CFAA regardless of the Van Buren narrowing. Risk level: high.
Creating Fake Accounts or Identities ToS violation at minimum, potentially fraudulent depending on purpose. Risk level: high.
Copyright Law and Scraped Content
Factual data itself is not copyrightable. Prices, specifications, addresses, and statistical figures are facts that anyone can collect and republish. But the specific way those facts are expressed (a uniquely written product description, an original photograph, a curated database with creative selection and arrangement) can be protected.
The US Supreme Court established in Feist Publications v. Rural Telephone Service (1991) that compilations of facts can be copyrighted only if they involve original selection, coordination, or arrangement. A straightforward alphabetical phone directory was not copyrightable. A creatively curated "best of" list might be.
For businesses scraping with proxies, the practical implication is simple. Collect the data, but don't wholesale copy the expression. Extract the price, the product name, the availability status. Don't copy the product description verbatim and republish it as your own. That distinction protects you from the most common copyright claims associated with web scraping.
Robots.txt: Legal Requirement or Polite Suggestion?
As of 2026, there is no US federal statute that makes violating robots.txt illegal per se. The robots.txt standard is a voluntary protocol, not a legal mandate. Courts have not held that ignoring robots.txt alone constitutes unauthorised access under the CFAA. In the hiQ case, the Ninth Circuit did not treat LinkedIn's robots.txt directives as creating legal barriers to access.
Robots.txt compliance still matters for several practical and legal reasons:
- It shows good faith. In any future litigation, showing that you respected robots.txt signals strengthens your argument that you acted reasonably
- It reduces server impact. Following crawl-delay directives minimises the risk that your scraping constitutes a tortious interference or trespass-to-chattels claim
- EU regulators may view robots.txt respect as part of responsible data processing under GDPR's accountability principle
- Some industry-specific regulations and standards reference robots.txt compliance as a baseline expectation
The pragmatic recommendation is to treat robots.txt as a strong default. Respect it unless you have a documented business justification and legal counsel's approval to deviate.
Building a Proxy Compliance Framework
1. Purpose Documentation For every scraping or data collection project, document the legitimate business purpose before you begin. "Competitive price monitoring to ensure our pricing remains market-competitive" is a documented purpose. "Let's see what data we can get" is not.
2. Data Classification Protocol Classify the data you intend to collect before collection begins. Is it factual (prices, specifications)? Is it personal (names, emails)? Is it copyrighted (articles, images)? Each classification triggers different legal obligations.
3. Jurisdictional Assessment Identify which legal jurisdictions apply. If you're a US company scraping EU websites, GDPR applies to any personal data you collect. If you're scraping sites hosted in specific US states, state-level computer fraud statutes may apply.
4. Technical Compliance Measures Rate limit to avoid overwhelming target servers. Respect robots.txt by default. Log your access patterns for potential future audits. Use appropriate headers that identify your scraping agent when possible.
5. Data Retention and Minimisation Collect only the data you need. Establish retention periods. Delete data when it's no longer necessary for its documented purpose. Particularly important under GDPR, but good practice universally.
6. Regular Review Cycle Laws change. Court rulings evolve. Review your compliance framework at least annually, and whenever a significant legal development occurs in this space.
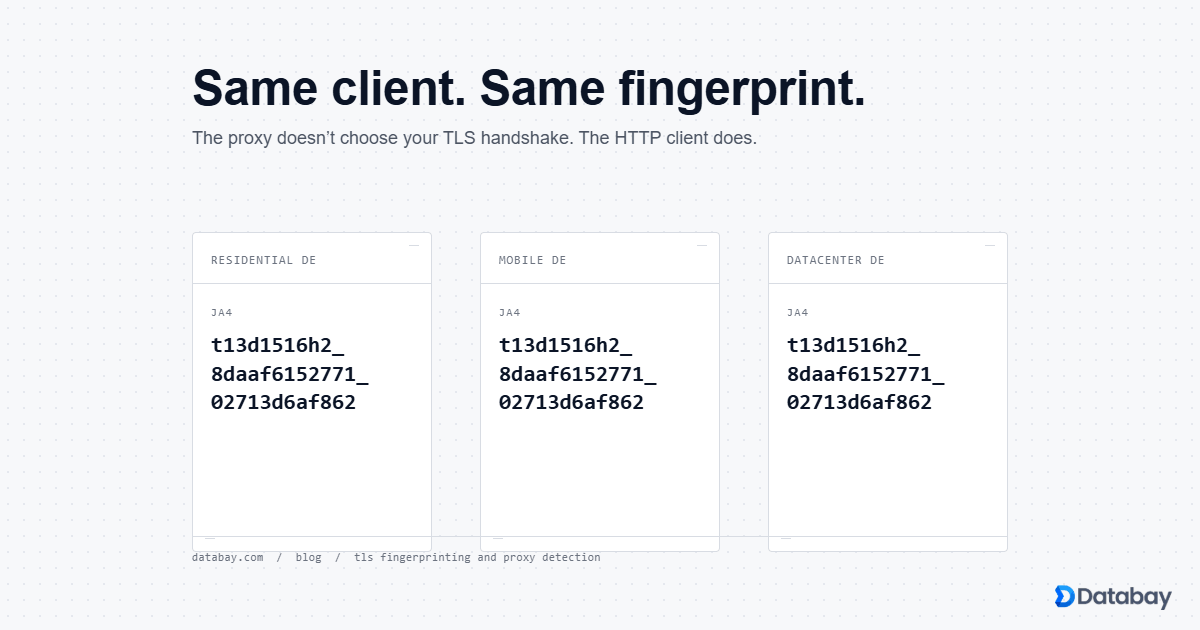
Residential vs. Datacenter Proxies: Any Legal Difference?
Datacenter proxies route traffic through servers in commercial data centres. Straightforward infrastructure with no special legal considerations beyond the general rules above. No third party's device or connection is involved.
Residential proxies route traffic through IP addresses assigned to real residential internet connections. The legal consideration here is about sourcing: how did the proxy provider obtain access to those residential IPs? Ethical providers use opt-in models where device owners knowingly consent to share their bandwidth, typically in exchange for a free app or service. This consent-based model is legally sound.
Providers who source residential IPs through malware, deceptive bundling, or without meaningful user consent create risk not just for themselves but potentially for their customers. If a regulator or plaintiff can show that the proxy infrastructure was built on deceptive practices, downstream users may face reputational and legal exposure.
When selecting a proxy provider, verify their IP sourcing practices. Ask for documentation of their consent mechanisms. A reputable provider should be transparent about how residential IPs enter their network. At Databay, every residential IP in our network comes from devices whose owners have explicitly opted in through clear, informed consent.
When You Need Legal Counsel
- Before scraping at enterprise scale If your operation will make millions of requests per day or target dozens of major platforms, get legal review of your specific plan
- When collecting personal data in the EU GDPR compliance requires specific legal analysis of your lawful basis, data protection impact, and cross-border transfer mechanisms
- After receiving a cease-and-desist letter Don't ignore these. Have counsel assess your legal position and craft an appropriate response
- When your use case involves regulated industries Financial services, healthcare, and government data have additional regulatory layers beyond general computer access and privacy law
- When scraping copyrighted content If your business model depends on using content from other sites (not just factual data), you need a fair use analysis specific to your situation
- Before entering new geographic markets Data protection and computer access laws vary significantly across jurisdictions, including within regions like the EU where member states have implemented GDPR differently
The cost of proactive legal advice is invariably lower than the cost of reactive litigation defence. Budget for it as an operational expense, not an afterthought.
Practical Takeaways for Business Proxy Users
Do use proxies for competitive intelligence, price monitoring, ad verification, and market research on publicly available data. Well-established, legally supported use cases.
Do document your legitimate business purpose for every data collection activity. Written records of intent are your best defence in any future dispute.
Do respect rate limits and implement reasonable crawl delays. Server impact is a factor in trespass-to-chattels claims and demonstrates good faith.
Do classify data before collection and apply GDPR safeguards when collecting personal data from EU sources.
Do choose proxy providers with transparent, ethical IP sourcing practices.
Don't bypass login pages, CAPTCHAs designed to gate non-public content, or authentication systems.
Don't scrape and republish copyrighted content wholesale.
Don't collect personal data beyond what's necessary for your stated purpose.
Don't assume US legal standards apply globally. GDPR, the EU Digital Services Act, and other international frameworks create additional obligations.
Proxies are legal. Responsible use keeps them that way. The businesses that build compliance into their data collection operations from the start are the ones that scale without legal disruption.